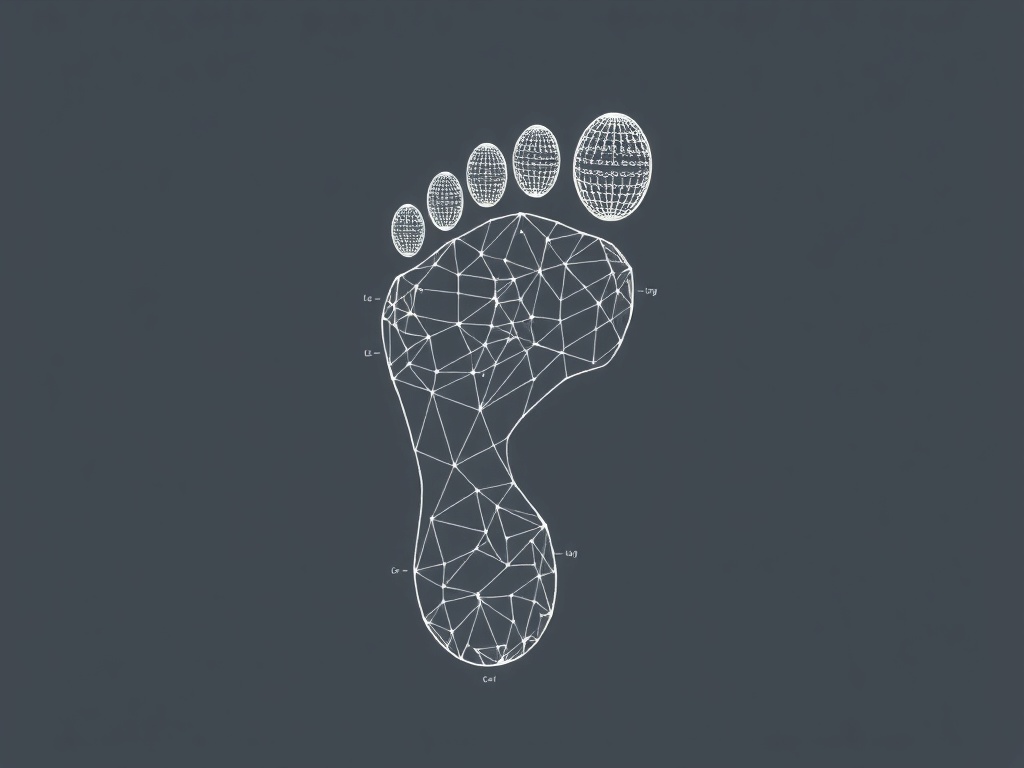
Your digital footprint is the trail of data you leave behind whenever you use the internet — from social posts and online purchases to background tracking by websites and apps.
Understanding and managing that footprint protects privacy, strengthens security, and preserves reputation across personal and professional spheres.
What makes up a digital footprint
– Active footprint: content you intentionally create or share, such as social updates, blog posts, comments, and uploads.
– Passive footprint: data collected without direct action, including tracking cookies, IP addresses, location signals, metadata, and third-party data broker profiles.
Why it matters
Every piece of data contributes to how you appear in search results, how advertisers profile you, and how easily malicious actors can exploit personal information. Left unchecked, outdated profiles, exposed credentials, or excessive permissions can lead to identity theft, phishing, or long-term reputational damage.
Practical steps to shrink and manage your footprint
1. Audit what’s out there
– Search your name and common email addresses on major search engines and review the first few pages of results. Check image searches and social media mentions. Note anything inaccurate, sensitive, or unnecessary.
2.
Tighten privacy settings
– Review privacy and sharing settings on social platforms, cloud services, and devices. Limit visibility of posts and personal details to trusted contacts only. Adjust ad personalization settings where available.
3. Clean up old accounts and content
– Delete or deactivate accounts you no longer use. Remove old posts, tags, and photos that no longer reflect how you want to be seen. For services without straightforward deletion, contact support or follow available opt-out procedures.
4. Reduce data sharing
– Use throwaway or alias email addresses for newsletters and trial services.
Avoid signing up with social logins unless necessary.
Minimize granting permissions to apps; deny access to contacts, location, or microphone when unrelated to the app’s core function.
5. Lock down access credentials
– Use long, unique passwords and a reputable password manager. Enable two-factor authentication for email, social accounts, and financial services to add an extra layer of security.
6.
Control tracking and cookies
– Use privacy-focused browsers or browser extensions to block trackers and third-party cookies. Regularly clear cookies and browser history or use private browsing modes for sessions you don’t want stored.
7. Opt out of data broker listings
– Data brokers aggregate and sell personal data. Many offer opt-out mechanisms; submitting requests can reduce the number of public profiles tied to your name and contact details.
8. Be cautious with public Wi‑Fi and shared devices
– Avoid accessing sensitive accounts on public networks without a VPN. Log out and clear browsing data after using shared devices.
Legal rights and professional help
Data protection laws in many regions grant rights such as access to your personal data, correction, and deletion. Use these rights where available. For complex reputation issues or persistent doxxing, consider consulting privacy professionals or legal counsel.
A mindset for long-term control
Treat digital hygiene like physical hygiene: routine, consistent, and preventive. Before sharing anything online, consider whether it’s something you’d be comfortable with strangers, future employers, or automated profiling systems seeing. Regular audits, cautious sharing, and sensible security practices keep your digital footprint working for you rather than against you.
Take action now: run a quick search on yourself, update high-risk privacy settings, and adopt one new protective habit this week to reclaim control of your online presence.