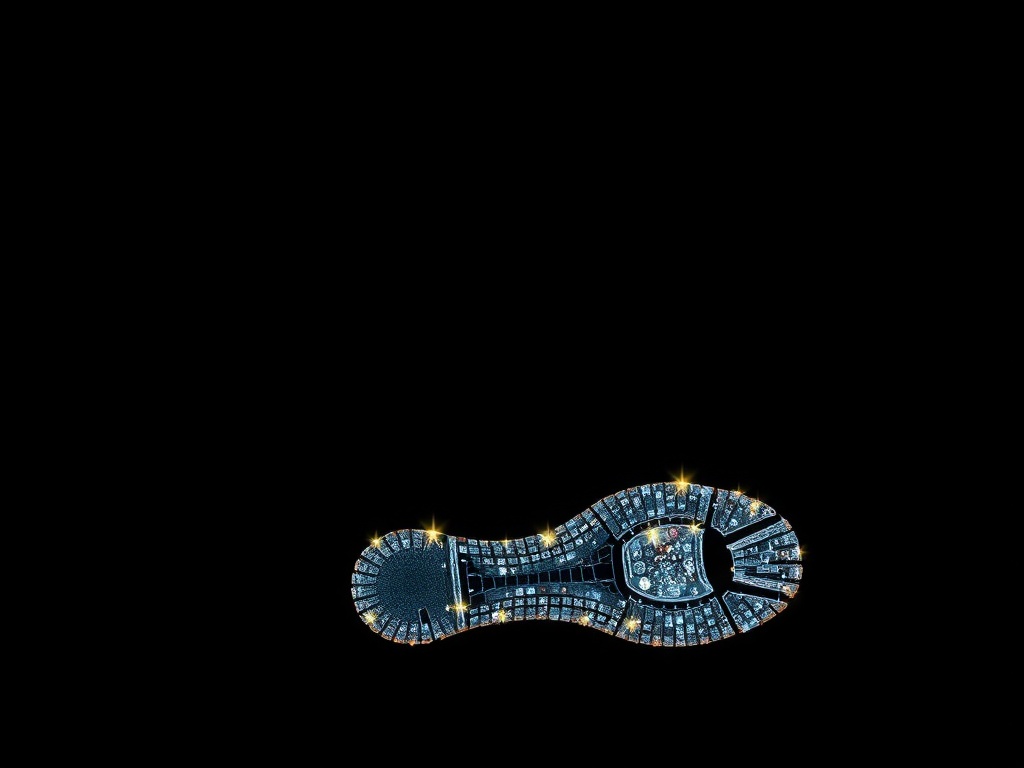
Digital footprint describes the trail of data you leave online every time you browse, post, shop, or communicate. That trail includes obvious actions—social media posts, comments, photos—and less visible traces like search history, metadata, cookies, and information collected by apps and devices. Understanding and managing your digital footprint is essential for privacy, reputation, and security.
Why it matters
A large or poorly managed digital footprint can affect personal privacy, job prospects, insurance and loan decisions, targeted advertising, and even identity theft risk. Recruiters and automated screening tools often scan online profiles.
Advertisers and data brokers compile behavioral profiles that influence what you see and who can access your data. Devices connected to the internet also share telemetry that contributes to your passive footprint.
Types of digital footprints
– Active footprint: Content you intentionally publish—posts, uploads, forum comments, reviews, and public profiles.
– Passive footprint: Data collected without explicit posting—cookies, location logs, browsing history, device telemetry, and data broker profiles.
– Residual footprint: Old accounts, cached content, and metadata embedded in files that persist even after deletion.
Practical steps to audit and reduce your footprint
1. Search for yourself regularly: Use multiple search engines and vary query terms (name, email, phone) to see what’s publicly available. Set up alerts for new mentions if you want ongoing monitoring.
2. Tighten privacy settings: Review the privacy and visibility settings on social platforms, cloud services, and photo-sharing sites.
Limit profile visibility and remove public access to sensitive content.
3. Clean up old accounts: Deactivate or delete accounts you no longer use.
Use account discovery tools from platforms or manually search email inboxes for signup confirmations.
4. Remove metadata: Strip location and camera metadata from photos before sharing. Many phones and photo editing apps offer options to remove EXIF data.
5. Minimize data shared with apps: Grant only necessary permissions to apps—deny location, microphone, or contact access unless required. Revoke permissions for apps you rarely use.
6. Use unique, strong passwords and two-factor authentication: A password manager helps create and remember unique credentials. Enable two-factor authentication for key accounts to reduce breach risk.
7.
Limit cookie and tracker exposure: Use browser settings or extensions that block third-party trackers and clear cookies regularly. Consider privacy-focused browsers and search engines for less tracking.
8. Be cautious with public Wi-Fi: Use a VPN on unsecured networks to protect traffic from eavesdropping. Avoid logging into important accounts on shared networks unless protected.
9. Opt out of data brokers: Many brokers list opt-out processes—request removal where possible.
Third-party services can help, but manual requests are often free.
10. Use email aliases and phone masking: Use separate email addresses for different purposes—one for banking, one for subscriptions, one for public interactions.
Consider temporary or masked phone numbers for signups.
Long-term habits to adopt
– Think before sharing: Treat anything posted publicly as potentially permanent. Avoid oversharing personal details like home address, birthdate, or travel plans.
– Regular audits: Schedule periodic checks of privacy settings, saved passwords, and public search results.
– Keep software updated: Security patches reduce the risk that devices leak data through vulnerabilities.
– Educate household members: Children’s and family members’ online behavior contributes to a household footprint—set boundaries and teach privacy basics.
Managing a digital footprint isn’t about total invisibility; it’s about deliberate control and minimizing unnecessary exposure. With routine auditing, thoughtful sharing, and basic security practices, you can reduce risks and keep online life aligned with privacy and reputation goals.